- Explore MCP Servers
- GhidraMCP-AI-rename
Ghidramcp Ai Rename
What is Ghidramcp Ai Rename
GhidraMCP-AI-rename is a rapid deployment script based on GhidraMCP that automates the bulk renaming of functions and exporting of function text files for easier AI parsing.
Use cases
Use cases include automating the renaming of functions in large codebases, preparing data for AI models, and enhancing the efficiency of reverse engineering tasks.
How to use
To use GhidraMCP-AI-rename, input your silicon-based flow key and run the script ‘ai_先运行仅重命名.py’ to rename all functions. After the renaming is complete, run ‘ai_再运行文件保存.py’ to save the files. Ensure to configure the MCP service for analysis with Cherry or Cursor.
Key features
Key features include batch renaming of functions, exporting function text files for AI analysis, and compatibility with Ghidra and MCP services.
Where to use
GhidraMCP-AI-rename is used in reverse engineering, software analysis, and any field that requires automated function renaming and data extraction from binaries.
Clients Supporting MCP
The following are the main client software that supports the Model Context Protocol. Click the link to visit the official website for more information.
Overview
What is Ghidramcp Ai Rename
GhidraMCP-AI-rename is a rapid deployment script based on GhidraMCP that automates the bulk renaming of functions and exporting of function text files for easier AI parsing.
Use cases
Use cases include automating the renaming of functions in large codebases, preparing data for AI models, and enhancing the efficiency of reverse engineering tasks.
How to use
To use GhidraMCP-AI-rename, input your silicon-based flow key and run the script ‘ai_先运行仅重命名.py’ to rename all functions. After the renaming is complete, run ‘ai_再运行文件保存.py’ to save the files. Ensure to configure the MCP service for analysis with Cherry or Cursor.
Key features
Key features include batch renaming of functions, exporting function text files for AI analysis, and compatibility with Ghidra and MCP services.
Where to use
GhidraMCP-AI-rename is used in reverse engineering, software analysis, and any field that requires automated function renaming and data extraction from binaries.
Clients Supporting MCP
The following are the main client software that supports the Model Context Protocol. Click the link to visit the official website for more information.
Content
Ghidra逆向
基于GhidraMcp的快速逆向脚本
使用qwen7b的高速处理性,批量进行函数重命名。再导出文件便于ai解析。
逆向重写推荐cursor,记得给cursor配置MCP服务。
项目要求:python>3.10
在脚本目录下运行pip install -r requirements.txt
Ghidra下载:https://github.com/NationalSecurityAgency/ghidra
JDK21+下载:https://www.oracle.com/java/technologies/javase/jdk21-archive-downloads.html
樱桃下载:https://www.cherry-ai.com/download
已知樱桃1.2.8-1.2.9的MCP服务器功能有bug,请下载1.2.10或更新的版本
Ghidra安装MCP插件:
https://github.com/user-attachments/assets/75f0c176-6da1-48dc-ad96-c182eb4648c3
使用说明
208行 SK-XXXXXX改为自己的硅基流动密钥,然后运行ai_先运行仅重命名.py
等待所有的FUN_xxxx函数重命名结束后,再运行ai_再运行文件保存.py
然后配置樱桃或者cursor的MCP进行分析即可。
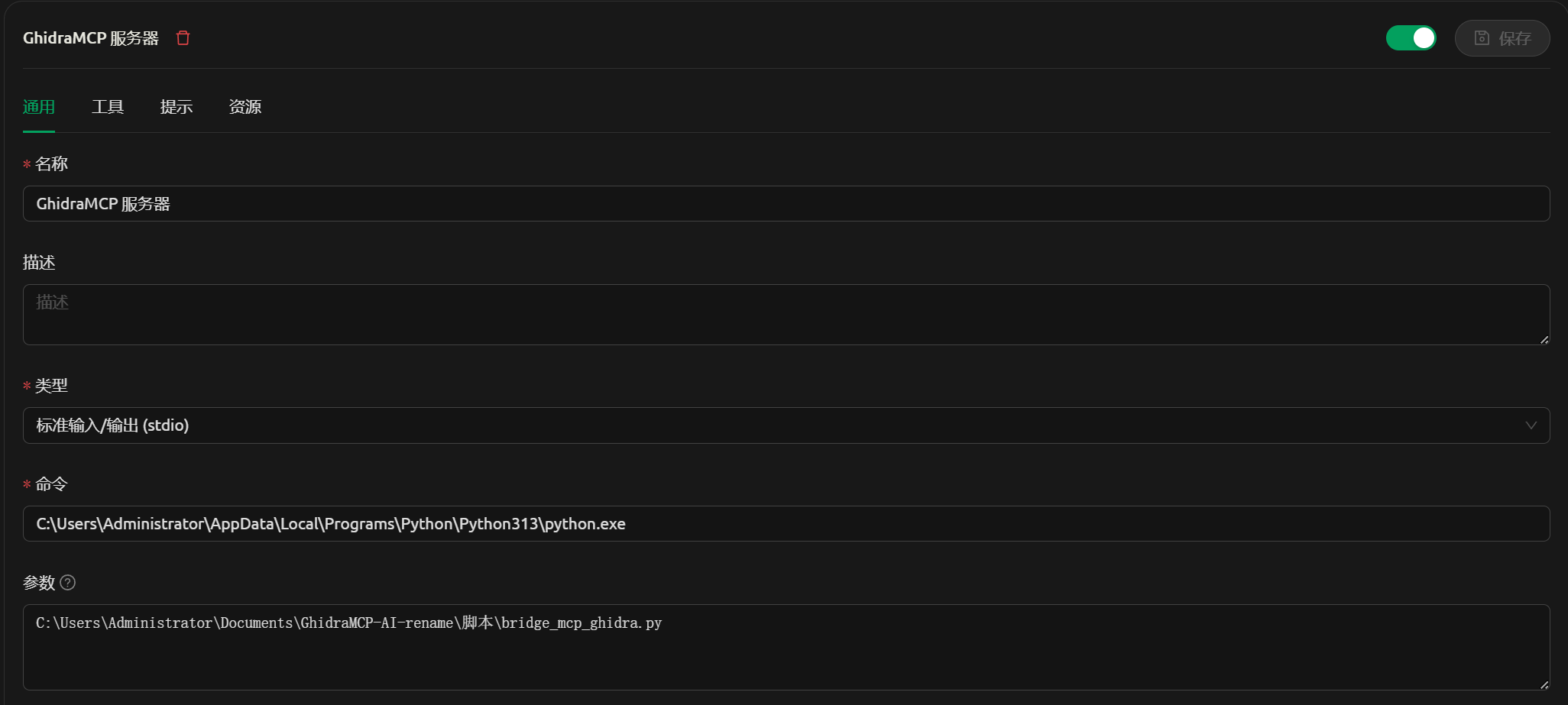
MCP配置中用到的python路径填已经装了依赖的路径,另一个填bridge_mcp_ghidra.py
的路径。
樱桃配置
command填写python路径,并使用双反斜杠,args填写bridge_mcp_ghidra.py的路径.
VS code 的cline配置
command填写python路径,并使用双反斜杠,args填写bridge_mcp_ghidra.py的路径.
{ "mcpServers": { "GhidraMCP": { "name": "GhidraMcp", "type": "stdio", "description": "", "isActive": true, "command": "C:\\Users\\Administrator\\AppData\\Local\\Programs\\Python\\Python313\\python.exe", "args": [ "C:\\Users\\Administrator\\Documents\\GhidraMCP-AI-rename\\脚本\\bridge_mcp_ghidra.py" ], "disabled": false, "autoApprove": [ "list_imports" ] } } }
Cursor配置:
command填写python路径,并使用双反斜杠,args填写bridge_mcp_ghidra.py的路径.
{
"mcpServers": {
"GhidraMcp": {
"name": "GhidraMcp",
"type": "stdio",
"description": "",
"isActive": true,
"command": "C:\\Users\\Administrator\\AppData\\Local\\Programs\\Python\\Python313\\python.exe",
"args": [
"C:\\Users\\Administrator\\Downloads\\Compressed\\ghidra_11.3.1_PUBLIC_20250219\\bridge_mcp_ghidra.py"
]
}
}
}小工具
需要远程协助配置请发送邮件到:
[email protected]
Dev Tools Supporting MCP
The following are the main code editors that support the Model Context Protocol. Click the link to visit the official website for more information.










