- Explore MCP Servers
- mcp-security-audit
Mcp Security Audit
What is Mcp Security Audit
mcp-security-audit is a powerful MCP (Model Context Protocol) Server designed to audit npm package dependencies for security vulnerabilities. It integrates with remote npm registries to perform real-time security checks.
Use cases
Use cases for mcp-security-audit include ensuring the security of npm package dependencies in software projects, performing regular security audits, and providing developers with actionable insights and recommendations to mitigate vulnerabilities.
How to use
To use mcp-security-audit, you can install it via Smithery using the command: npx -y @smithery/cli install @qianniuspace/mcp-security-audit --client claude. Alternatively, you can clone the repository, install dependencies, and configure it manually.
Key features
Key features include real-time security vulnerability scanning, remote npm registry integration, detailed vulnerability reports with severity levels, support for multiple severity levels (critical, high, moderate, low), compatibility with npm/pnpm/yarn package managers, automatic fix recommendations, and CVSS scoring with CVE references.
Where to use
undefined
Clients Supporting MCP
The following are the main client software that supports the Model Context Protocol. Click the link to visit the official website for more information.
Overview
What is Mcp Security Audit
mcp-security-audit is a powerful MCP (Model Context Protocol) Server designed to audit npm package dependencies for security vulnerabilities. It integrates with remote npm registries to perform real-time security checks.
Use cases
Use cases for mcp-security-audit include ensuring the security of npm package dependencies in software projects, performing regular security audits, and providing developers with actionable insights and recommendations to mitigate vulnerabilities.
How to use
To use mcp-security-audit, you can install it via Smithery using the command: npx -y @smithery/cli install @qianniuspace/mcp-security-audit --client claude. Alternatively, you can clone the repository, install dependencies, and configure it manually.
Key features
Key features include real-time security vulnerability scanning, remote npm registry integration, detailed vulnerability reports with severity levels, support for multiple severity levels (critical, high, moderate, low), compatibility with npm/pnpm/yarn package managers, automatic fix recommendations, and CVSS scoring with CVE references.
Where to use
undefined
Clients Supporting MCP
The following are the main client software that supports the Model Context Protocol. Click the link to visit the official website for more information.
Content
Security Audit Tool
A powerful MCP (Model Context Protocol) Server that audits npm package dependencies for security vulnerabilities. Built with remote npm registry integration for real-time security checks.
Features
- 🔍 Real-time security vulnerability scanning
- 🚀 Remote npm registry integration
- 📊 Detailed vulnerability reports with severity levels
- 🛡️ Support for multiple severity levels (critical, high, moderate, low)
- 📦 Compatible with npm/pnpm/yarn package managers
- 🔄 Automatic fix recommendations
- 📋 CVSS scoring and CVE references
Installing via Smithery
To install Security Audit Tool for Claude Desktop automatically via Smithery:
npx -y @smithery/cli install @qianniuspace/mcp-security-audit --client claude
MCP Integration
Option 1: Using NPX (Recommended)
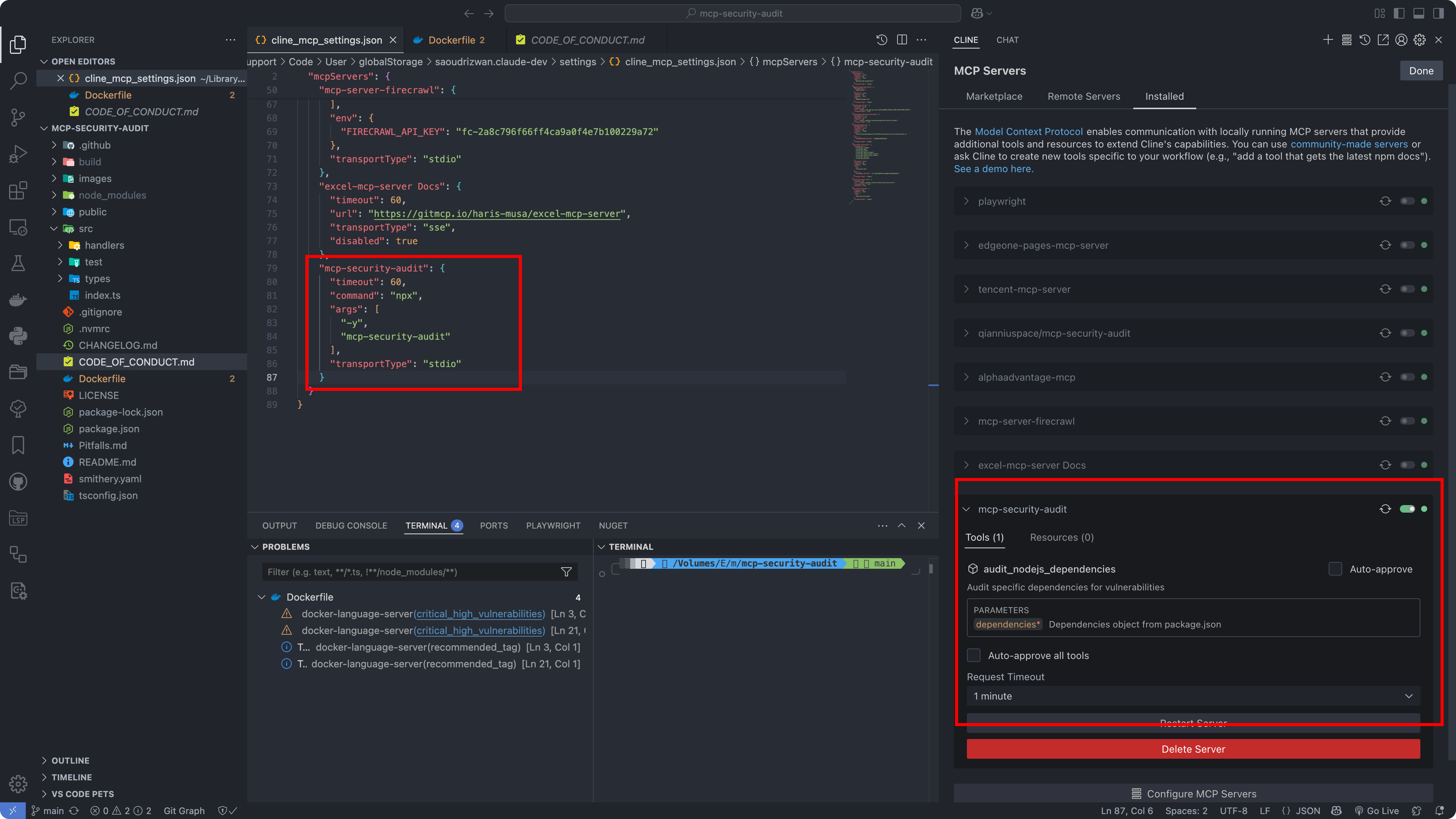
- Add MCP configuration to Cline /Cursor:
{
"mcpServers": {
"mcp-security-audit": {
"command": "npx",
"args": [
"-y",
"mcp-security-audit"
]
}
}
}Option 2: Download Source Code and Configure Manually
- Clone the repository:
git clone https://github.com/qianniuspace/mcp-security-audit.git
cd mcp-security-audit
- Install dependencies and build:
npm install npm run build
- Add MCP configuration to Cline /Cursor :
{
"mcpServers": {
"mcp-security-audit": {
"command": "npx",
"args": [
"-y",
"/path/to/mcp-security-audit/build/index.js"
]
}
}
}Configuration Screenshots
Cursor Configuration
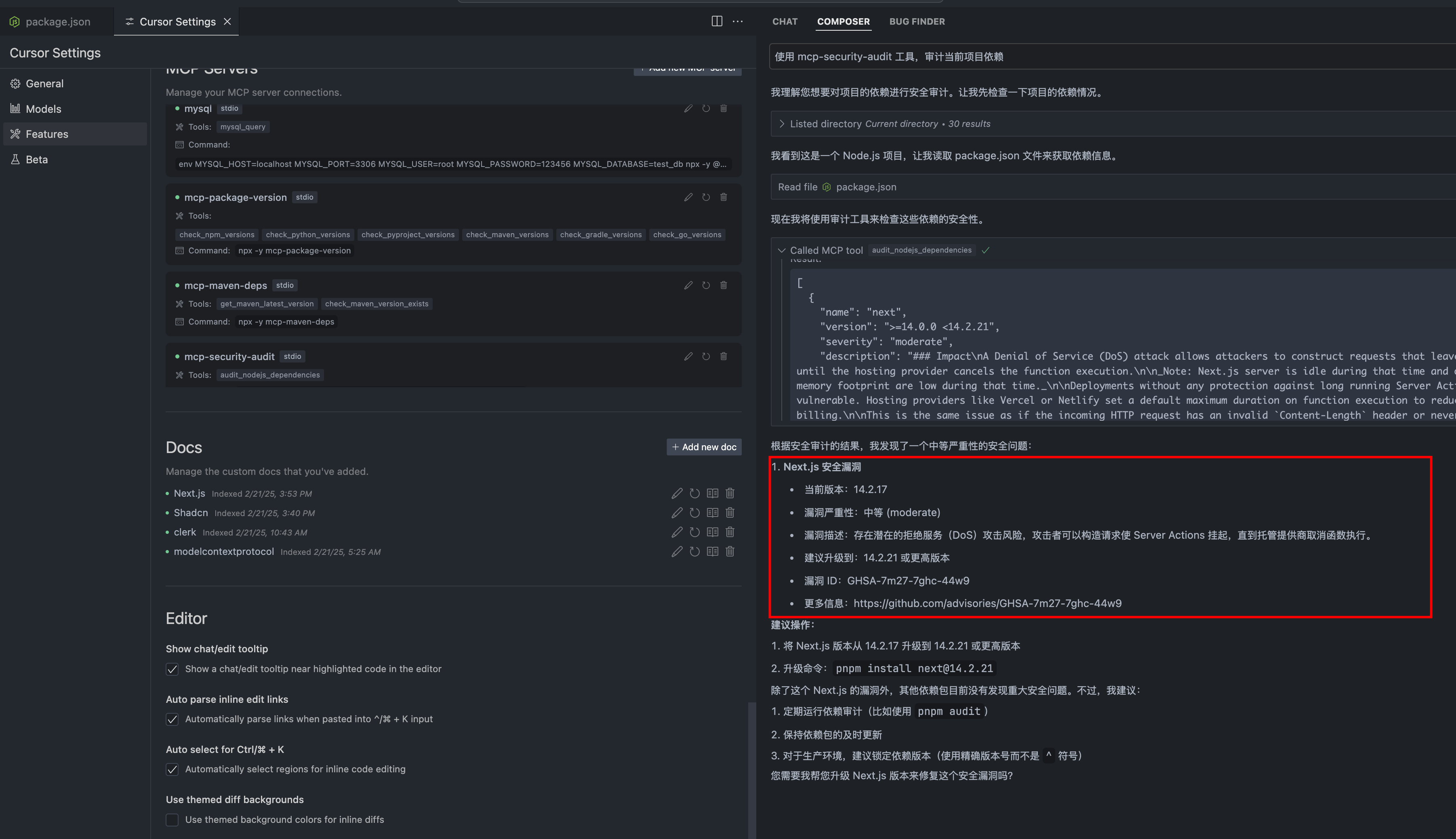
Cline Configuration
API Response Format
The tool provides detailed vulnerability information including severity levels, fix recommendations, CVSS scores, and CVE references.
Response Examples
1. When Vulnerabilities Found (Severity-response.json)
{
"content": [
{
"vulnerability": {
"packageName": "lodash",
"version": "4.17.15",
"severity": "high",
"description": "Prototype Pollution in lodash",
"cve": "CVE-2020-8203",
"githubAdvisoryId": "GHSA-p6mc-m468-83gw",
"recommendation": "Upgrade to version 4.17.19 or later",
"fixAvailable": true,
"fixedVersion": "4.17.19",
"cvss": {
"score": 7.4,
"vector": "CVSS:3.1/AV:N/AC:H/PR:N/UI:N/S:U/C:H/I:H/A:N"
},
"cwe": [
"CWE-1321"
],
"url": "https://github.com/advisories/GHSA-p6mc-m468-83gw"
},
"metadata": {
"timestamp": "2024-04-23T10:00:00.000Z",
"packageManager": "npm"
}
}
]
}2. When No Vulnerabilities Found (no-Severity-response.json)
{
"content": [
{
"vulnerability": null,
"metadata": {
"timestamp": "2024-04-23T10:00:00.000Z",
"packageManager": "npm",
"message": "No known vulnerabilities found"
}
}
]
}Development
For development reference, check the example response files in the public directory:
- Severity-response.json : Example response when vulnerabilities are found (transformed from npm audit API response)
- no-Severity-response.json : Example response when no vulnerabilities are found (transformed from npm audit API response)
Note: The example responses shown above are transformed from the raw npm audit API responses to provide a more structured format. The original npm audit API responses contain additional metadata and may have a different structure.
Contributing
Contributions are welcome! Please read our Contributing Guide for details on our code of conduct and the process for submitting pull requests.
License
This project is licensed under the MIT License - see the LICENSE file for details.
Author
ESX ([email protected])
Links
Dev Tools Supporting MCP
The following are the main code editors that support the Model Context Protocol. Click the link to visit the official website for more information.